Terraform’s Latest Features: Cost Analytics, Project-Level Notifications, and Enhanced Governance
In recent months, HashiCorp Terraform has rolled out a suite of improvements designed to give organizations clearer cost visibility, stronger governance, and better security across their infrastructure lifecycle. The new features include general availability of billable resource analytics, project-level remote state sharing, module testing for dynamic credentials, project-level notifications, and a beta for registry tagging. This article answers key questions about these updates and how they can help your team eliminate blind spots and optimize operations.
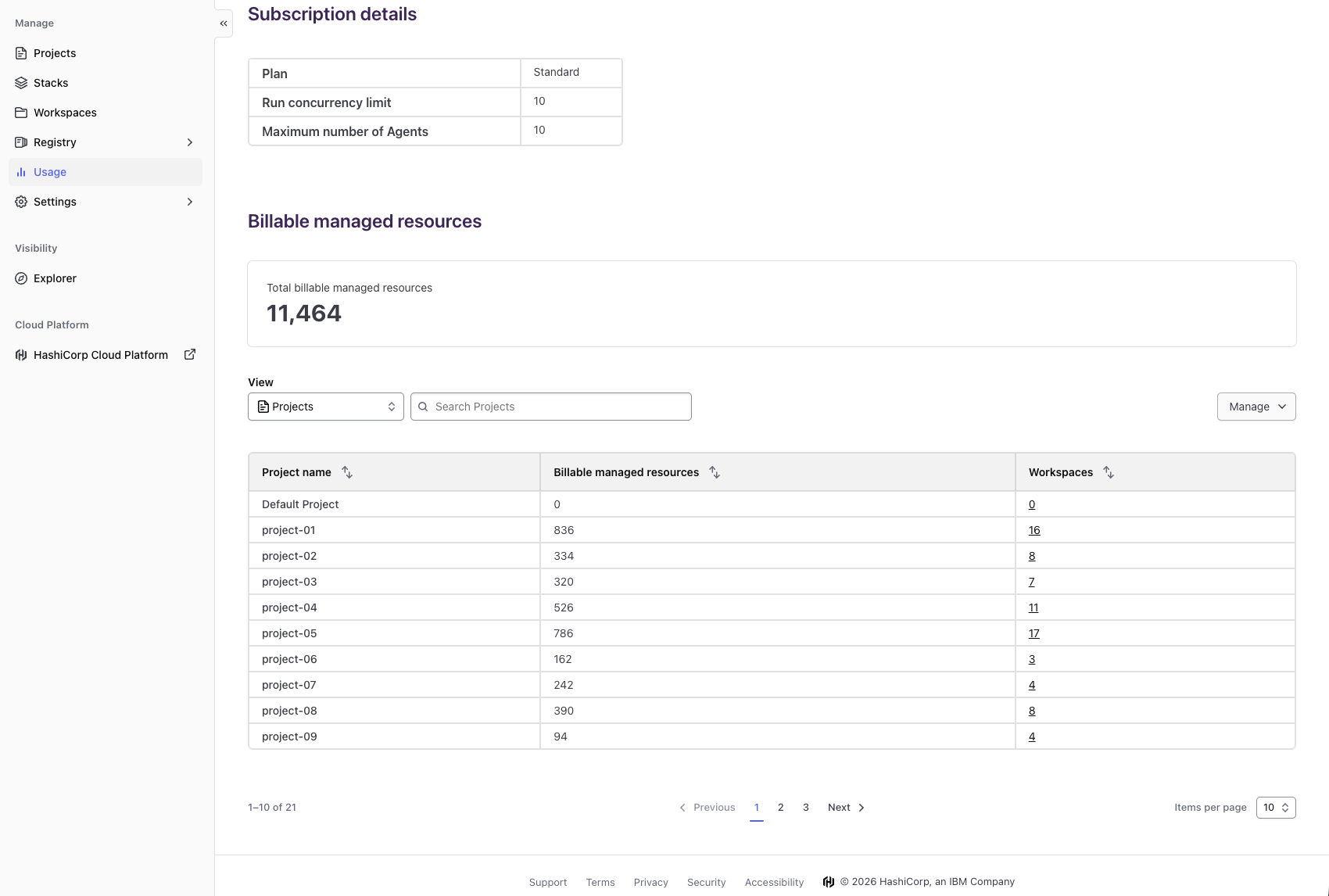
What is billable resource analytics and how does it improve cost management?
Billable resource analytics, now generally available in HCP Terraform, provides a comprehensive breakdown of resource consumption at the project and workspace level. Previously, organizations using resources-under-management (RUM) billing could only see total costs at the organization level, making it difficult to pinpoint where spending was happening. With this new feature, decision makers can view detailed analytics on the existing usage page, identifying high-consumption projects and workspaces. This visibility enables proactive cost management, allowing teams to right-size resources, eliminate waste, and stay within budgets. It also supports data-driven decisions—leaders can align infrastructure investments with business priorities based on actual consumption patterns rather than guesswork. Ultimately, billable resource analytics turns cost data from a black box into a strategic tool for optimization.
How does project-level remote state sharing benefit platform teams?
Project-level remote state sharing, now generally available, solves a common dilemma for platform teams managing large-scale infrastructure. Previously, sharing state data between projects forced a trade-off: centralize all state in one project (causing security and scaling issues) or duplicate state across projects (leading to inconsistency and extra work). The new feature allows teams to share state selectively at the project level, granting access only where needed. This maintains security boundaries while enabling collaboration—for example, one project can consume outputs from another without copying data. It reduces operational overhead and prevents version drift, making multi-project workflows smoother and more reliable. Teams can now build modular architectures with confidence, knowing that state is shared exactly as intended without exposing sensitive information.
What is module testing for dynamic credentials and why is it important?
Module testing for dynamic credentials, now generally available, enhances security by allowing teams to test Terraform modules that use dynamic provider credentials. In many organizations, modules rely on short-lived credentials (e.g., from Vault or AWS STS) rather than static keys. Without proper testing, these modules risk exposing credentials or failing in production due to permission issues. This feature integrates credential lifecycle management into the testing process, ensuring that modules can handle dynamic authentication correctly before deployment. It reduces security blind spots by catching misconfigurations early, and it streamlines continuous integration pipelines. Developers can iterate confidently, knowing that their modules will work seamlessly with the organization’s security policies. This capability is especially valuable for teams adopting zero-trust architectures where static credentials are avoided.
How do project-level notifications improve governance?
Project-level notifications, now generally available, give teams granular control over alerts. Previously, notifications (e.g., run failures or policy violations) were limited to the organization level, meaning every team member received alerts for all projects—even irrelevant ones. This caused alert fatigue and delayed responses to critical issues. With project-level notifications, administrators can set specific alert rules per project, sending them only to the relevant team. For example, the networking team can be notified only when a network workspace run fails, while the security team receives only policy violation alerts. This targeted approach improves incident response times, reduces noise, and strengthens compliance by ensuring the right people are informed at the right time. It also supports better audit trails because notifications are scoped to project boundaries.
What is registry tagging and how does it help manage modules?
Registry tagging, currently in beta, is a new capability in the Terraform Registry that allows module authors to attach descriptive tags to their published modules. Tags are metadata labels (e.g., “networking,” “production-ready,” “security”) that make it easier for users to discover, filter, and organize modules. For organizations with large private registries, tagging reduces the time spent searching for the right module by categorizing resources based on function, team, or compliance level. It also enables better governance—platform teams can enforce naming conventions or require specific tags for modules to be used in production. Tagging works alongside existing versioning and documentation, creating a richer discovery experience. As a beta feature, teams are encouraged to try it in non-critical environments and provide feedback, with full production support expected in a future release.